Order Now
- Home
- About Us
-
Services
-
Assignment Writing
-
Academic Writing Services
- HND Assignment Help
- SPSS Assignment Help
- College Assignment Help
- Writing Assignment for University
- Urgent Assignment Help
- Architecture Assignment Help
- Total Assignment Help
- All Assignment Help
- My Assignment Help
- Student Assignment Help
- Instant Assignment Help
- Cheap Assignment Help
- Global Assignment Help
- Write My Assignment
- Do My Assignment
- Solve My Assignment
- Make My Assignment
- Pay for Assignment Help
-
Management
- Management Assignment Help
- Business Management Assignment Help
- Financial Management Assignment Help
- Project Management Assignment Help
- Supply Chain Management Assignment Help
- Operations Management Assignment Help
- Risk Management Assignment Help
- Strategic Management Assignment Help
- Logistics Management Assignment Help
- Global Business Strategy Assignment Help
- Consumer Behavior Assignment Help
- MBA Assignment Help
- Portfolio Management Assignment Help
- Change Management Assignment Help
- Hospitality Management Assignment Help
- Healthcare Management Assignment Help
- Investment Management Assignment Help
- Market Analysis Assignment Help
- Corporate Strategy Assignment Help
- Conflict Management Assignment Help
- Marketing Management Assignment Help
- Strategic Marketing Assignment Help
- CRM Assignment Help
- Marketing Research Assignment Help
- Human Resource Assignment Help
- Business Assignment Help
- Business Development Assignment Help
- Business Statistics Assignment Help
- Business Ethics Assignment Help
- 4p of Marketing Assignment Help
- Pricing Strategy Assignment Help
- Nursing
-
Finance
- Finance Assignment Help
- Do My Finance Assignment For Me
- Financial Accounting Assignment Help
- Behavioral Finance Assignment Help
- Finance Planning Assignment Help
- Personal Finance Assignment Help
- Financial Services Assignment Help
- Forex Assignment Help
- Financial Statement Analysis Assignment Help
- Capital Budgeting Assignment Help
- Financial Reporting Assignment Help
- International Finance Assignment Help
- Business Finance Assignment Help
- Corporate Finance Assignment Help
-
Accounting
- Accounting Assignment Help
- Managerial Accounting Assignment Help
- Taxation Accounting Assignment Help
- Perdisco Assignment Help
- Solve My Accounting Paper
- Business Accounting Assignment Help
- Cost Accounting Assignment Help
- Taxation Assignment Help
- Activity Based Accounting Assignment Help
- Tax Accounting Assignment Help
- Financial Accounting Theory Assignment Help
-
Computer Science and IT
- Operating System Assignment Help
- Data mining Assignment Help
- Robotics Assignment Help
- Computer Network Assignment Help
- Database Assignment Help
- IT Management Assignment Help
- Network Topology Assignment Help
- Data Structure Assignment Help
- Business Intelligence Assignment Help
- Data Flow Diagram Assignment Help
- UML Diagram Assignment Help
- R Studio Assignment Help
-
Law
- Law Assignment Help
- Business Law Assignment Help
- Contract Law Assignment Help
- Tort Law Assignment Help
- Social Media Law Assignment Help
- Criminal Law Assignment Help
- Employment Law Assignment Help
- Taxation Law Assignment Help
- Commercial Law Assignment Help
- Constitutional Law Assignment Help
- Corporate Governance Law Assignment Help
- Environmental Law Assignment Help
- Criminology Assignment Help
- Company Law Assignment Help
- Human Rights Law Assignment Help
- Evidence Law Assignment Help
- Administrative Law Assignment Help
- Enterprise Law Assignment Help
- Migration Law Assignment Help
- Communication Law Assignment Help
- Law and Ethics Assignment Help
- Consumer Law Assignment Help
- Science
- Biology
- Engineering
-
Humanities
- Humanities Assignment Help
- Sociology Assignment Help
- Philosophy Assignment Help
- English Assignment Help
- Geography Assignment Help
- Agroecology Assignment Help
- Psychology Assignment Help
- Social Science Assignment Help
- Public Relations Assignment Help
- Political Science Assignment Help
- Mass Communication Assignment Help
- History Assignment Help
- Cookery Assignment Help
- Auditing
- Mathematics
-
Economics
- Economics Assignment Help
- Managerial Economics Assignment Help
- Econometrics Assignment Help
- Microeconomics Assignment Help
- Business Economics Assignment Help
- Marketing Plan Assignment Help
- Demand Supply Assignment Help
- Comparative Analysis Assignment Help
- Health Economics Assignment Help
- Macroeconomics Assignment Help
- Political Economics Assignment Help
- International Economics Assignments Help
-
Academic Writing Services
-
Essay Writing
- Essay Help
- Essay Writing Help
- Essay Help Online
- Online Custom Essay Help
- Descriptive Essay Help
- Help With MBA Essays
- Essay Writing Service
- Essay Writer For Australia
- Essay Outline Help
- illustration Essay Help
- Response Essay Writing Help
- Professional Essay Writers
- Custom Essay Help
- English Essay Writing Help
- Essay Homework Help
- Literature Essay Help
- Scholarship Essay Help
- Research Essay Help
- History Essay Help
- MBA Essay Help
- Plagiarism Free Essays
- Writing Essay Papers
- Write My Essay Help
- Need Help Writing Essay
- Help Writing Scholarship Essay
- Help Writing a Narrative Essay
- Best Essay Writing Service Canada
-
Dissertation
- Biology Dissertation Help
- Academic Dissertation Help
- Nursing Dissertation Help
- Dissertation Help Online
- MATLAB Dissertation Help
- Doctoral Dissertation Help
- Geography Dissertation Help
- Architecture Dissertation Help
- Statistics Dissertation Help
- Sociology Dissertation Help
- English Dissertation Help
- Law Dissertation Help
- Dissertation Proofreading Services
- Cheap Dissertation Help
- Dissertation Writing Help
- Marketing Dissertation Help
- Programming
-
Case Study
- Write Case Study For Me
- Business Law Case Study Help
- Civil Law Case Study Help
- Marketing Case Study Help
- Nursing Case Study Help
- Case Study Writing Services
- History Case Study help
- Amazon Case Study Help
- Apple Case Study Help
- Case Study Assignment Help
- ZARA Case Study Assignment Help
- IKEA Case Study Assignment Help
- Zappos Case Study Assignment Help
- Tesla Case Study Assignment Help
- Flipkart Case Study Assignment Help
- Contract Law Case Study Assignments Help
- Business Ethics Case Study Assignment Help
- Nike SWOT Analysis Case Study Assignment Help
- Coursework
- Thesis Writing
- CDR
- Research
-
Assignment Writing
-
Resources
- Referencing Guidelines
-
Universities
-
Australia
- Asia Pacific International College Assignment Help
- Macquarie University Assignment Help
- Rhodes College Assignment Help
- APIC University Assignment Help
- Torrens University Assignment Help
- Kaplan University Assignment Help
- Holmes University Assignment Help
- Griffith University Assignment Help
- VIT University Assignment Help
- CQ University Assignment Help
-
Australia
- Experts
- Free Sample
- Testimonial
MIS607 Cybersecurity Assignment Sample
Assignment Brief
Assignment Title - MITIGATION PLAN FOR THREAT REPORT
Individual/Group - Individual
Length - 2500 words (+/- 10%)
Learning Outcomes:
The Subject Learning Outcomes demonstrated by successful completion of the task below include:
b) Explore and articulate cyber trends, threats and staying safe in cyberspace, plus protecting personal and company data.
c) Analyze issues associated with organizational data networks and security to recommend practical solutions towards their resolution.
d) Evaluate and communicate relevant technical and ethical considerations related to the design, deployment and/or the uses of secure technologies within various organizational contexts.
Submission - Due by 11:55pm AEST Sunday end of Module 6.1
Weighting - 45%
Total Marks - 100 marks
Task Summary
For this assessment, you are required to write a 2500 words mitigation plan for threat report based on knowledge you gained about threat types and key factors in Assessment 2. You are required to use the Assessment 2 case as context to write a report to address or alleviate problems faced by the business and to protect the customers. In doing so, you are required to demonstrate your ability to mitigate threat/risks identified in Assessment 2 through the strategy you recommend (STRIDE).
Context
Cybersecurity help organizations to mitigate threats/risks, reduce financial loss and safety violations, decrease unethical behaviour, improve customer satisfaction, and increase efficiency, as well as to maintain these improved results. Threats can be resolved by Risk Acceptance (doing nothing), Risk Transference (pass risk to an externality), Risk Avoidance (removing the feature/component that causes the risk) and Risk Mitigation (decrease the risk). This assessment gives you an opportunity to demonstrate your understanding of cybersecurity and your capability to explain Risk Mitigation strategies for such threats. Mitigations should be chosen according to the appropriate technology and resolution should be decided according to the risk level and cost of mitigation.
Task Instructions for assignment help
1. Read the Assessment 2 Case Scenario again to understand the concepts discussed in the case.
2. Review your subject notes to establish the relevant area of investigation that applies to the case. Re- read any relevant readings that have been recommended in the case area in modules. Plan how you will structure your ideas for the mitigation plan for threat report.
3. The mitigation plan for threat report should address the following:
• Setting priorities for risks/threats
• Analyze the case in terms of identified risk categories and scenarios
• Apply standard mitigations
• Discuss specific resolutions for improvement, and justify their significance
• Provide recommendations for mitigating risk based on an assessment of risk appetite, risk tolerance and current risk levels (Choose techniques to mitigate the threats)
• Make recommendations to the CEO on how to conduct risk management, key issues involving your process improvement model, including a road map, the identification of appropriate technologies for the identified techniques, communicating the strategy, and a suggested timeline.
4. The report should consist of the following structure:
A title page with subject code and name, assignment title, student’s name, student number, and lecturer’s name. The introduction that will also serve as your statement of purpose for the report. This means that you will tell the reader what you are going to cover in mitigation plan report. You will need to inform the reader of:
a) Your area of research and its context (how to mitigate or manage threats)
b) The key concepts you will be addressing
c) What the reader can expect to find in the body of the report
The body of the report will need to respond to the specific requirements of the case study. It is advised
that you use the case study to assist you in structuring the report. Set priorities for identified threats from assessment 2, analyze the case in terms of identified risk categories and discuss specific resolutions and recommendations for improvements in the body of the report.
The conclusion (will summarize any findings or recommendations that the report puts forward regarding the concepts covered in the report.
5. Format of the report
The report should use font Arial or Calibri 11 point, be line spaced at 1.5 for ease of reading, and have page numbers on the bottom of each page. If diagrams or tables are used, due attention should be given to pagination to avoid loss of meaning and continuity by unnecessarily splitting information over two pages. Diagrams must carry the appropriate captioning.
6. Referencing
There are requirements for referencing this report using APA referencing style for citing and referencing research. It is expected that you used 10 external references in the relevant subject area based on readings and further research. Please see more information on referencing here:https://library.torrens.edu.au/academic skills/apa/tool
7. You are strongly advised to read the rubric, which is an evaluation guide with criteria for grading the
assignment— this will give you a clear picture of what a successful report looks like.
Submission Instructions
Submit Assessment 3 via the Assessment link in the main navigation menu in MIS607 Cybersecurity. The Learning Facilitator will provide feedback via the Grade Centre in the LMS portal. Feedback can be viewed in My Grades.
Solution
Introduction
The purpose of this report is to prepare a mitigation plan for the identified threats from assessment-2 threat modelling report. The context of this report is based on the threat mitigation strategy, STRIDE which was recommended in the earlier assessment. In this threat report, it has been possible for me to address the key cybersecurity threats/risks faced by the Business & Communication (B&C) Insurance organisation and concept of risk acceptance, risk transference, risk avoidance, & risk mitigations. Moreover, in this report, recent cyber trends and relevant threats have been articulated and explored.
Readers can expect to learn about the risk mitigation strategies for critical cybersecurity threats through this assessment. Last, but not the least, this threat report helps the key stakeholders of B&C Insurance company to choose appropriate technology and resolution for the risk level. It also helps to understand the cost of mitigation and structured their own ideas for the same.
Threats Identification, Specific Resolution respond to the case study
Setting priorities for risks/threats
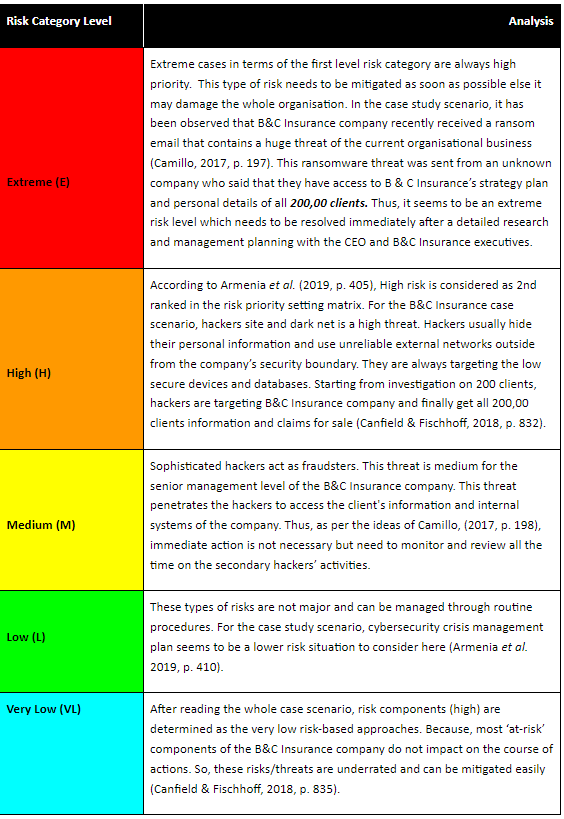
Table 1: Risk/Threat Prioritization (Source: Canfield & Fischhoff, 2018, p. 828)
Analysis in terms of risk categories and scenarios
Table 2: Analysis of identified threats for particular scenario (Source: Canfield & Fischhoff, 2018, p. 830)
Standard Mitigations
After knowing the risk categories and relevant scenarios for this B&C Insurance case study organisation, it is necessary to identify and apply standard mitigation techniques as follows:
? Installing Firewalls to protect email/website
Firewalls are enabled to protect B&C Insurance company websites. It has been designed to create a buffer between IT systems and external networks so that it can monitor the network traffic, block anything that could damage the computers, systems, and private networks (Armenia et al. 2019, p. 405). Firewalls also prevent cyber criminals from breaking down into networks and block outgoing traffic that contains a virus.
? Installing antivirus software
Installing antivirus acts as an essential technological defence for the B&C Insurance company. Modern range of antiviruses generally provide protection against a range of malware (spam emails), key loggers, ransomware, adware, spyware, and so on (Ganin et al. 2020, p. 185).
? Patch management
For software updates, need to fix the vulnerability along with a patch management plan.
? Cybersecurity risk assessment
As per the International standard: ISO 27001, step-by-step guidance has been followed for cyber security risk assessment. It is a standard mutation applied to gain benefits (Zadeh, Jeyaraj & Biros, 2020, p. 5).
? Information security policy
It is the result of risk assessment which has been adopted by the organisation itself to prevent unauthorized access. Information security policy will review the effectiveness of the control.
? Sensitive data encryption
As suggested by Zheng & Albert, (2019, p. 2078), Under the General Data Protection Regulation (GDPR), encrypted data cannot be assessed by the criminal or hackers even if they break the systems. It only accessed by the authorized personnel i.e. CEO of the B&C Insurance with a decryption key.
? Remote working policy
Create a remote working policy for the B&C Insurance employees reshaped the organisational security services. It recommends two-factor authentication to any third-party services for personal use (Armenia et al. 2019, p. 410).
? Conduct vulnerability scans
Vulnerability scanning improves the overall cybersecurity effectiveness and security measurements.
? Create a different business continuity plan for B&C Insurance
It is also a standard mitigation that outlines the critical processes of an organisational operation in the event of a major disruption (Ganin et al. 2020, p. 188).
? Conducting penetration test
It is important to resist hacking on behalf of the B&C Insurance company. Automated scans enable the actors and leverage the weaknesses to gain a true insight. Penetration test is important to stop criminals, ethical hackers and implement defences (Zadeh, Jeyaraj & Biros, 2020, p. 12).
Specific Resolutions
After considering the cybersecurity threats for B&C Insurance company and discussing the standard mitigations, it has been possible for me to describe specific resolutions for improvement and justify their significance for the same. The following are the resolutions for B&C Insurance companies which can be implemented to ensure that the organisation does not become the victim of cyber-crime, hackers, or fraudsters (Zheng & Albert, 2019, p. 2080).
? Providing security training is a best resolution that aware the employees before clicking a malicious link or downloading fraudulent software.
? Updated strong anti-virus software is useful to protect internal organisational data (Armenia et al. 2019, p. 413).
? How to respond to the phishing threats from exploitation of software vulnerabilities has also to be considered.
? Strong password policy is a resolution to the threats and risks faced by the B&C Insurance company.
? As per the guidance of Ganin et al. (2020, p. 190), multi factor authentication is a resolution that allows B&C Insurance company to protect its compromised credentials. Attempting corporate applications, networks, and servers is also a resolution approach.
? Backing-up databases is also important. It could be the essential solution when the company lost almost its data after a cyber-attack (Zadeh, Jeyaraj & Biros, 2020, p. 20).
Recommendations for Risk Mitigation
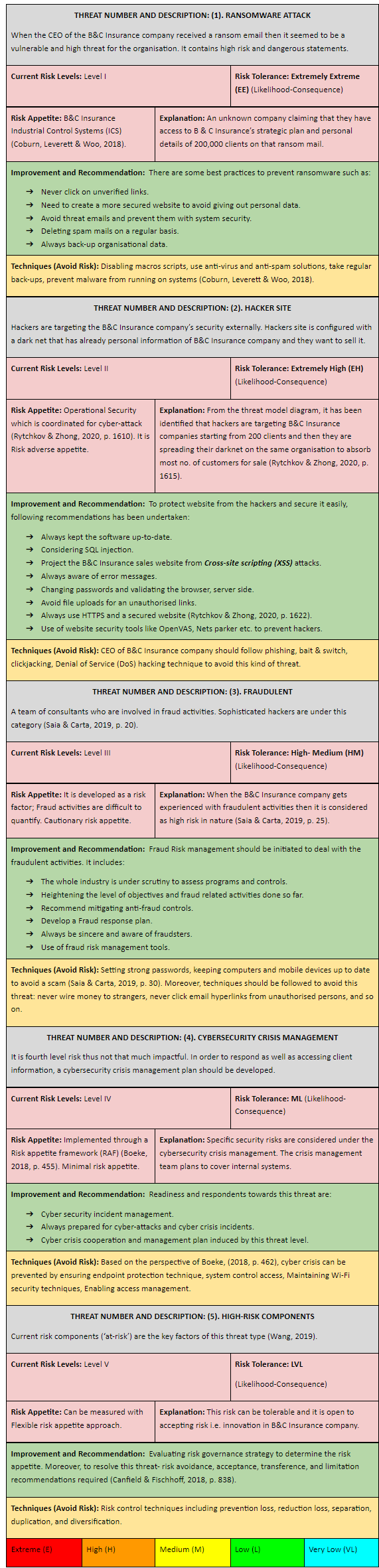
Table 3: Mitigating Risk Assessment (Source: Wang, 2019)
Risk Management Roadmap
In this stage, on the basis of risk categories and key issues involved to the threat model a risk management has been conducted. It is included in the following table.
Table 4: Risk Management approaches and relevant criterions (Source:

Figure 1: Risk Roadmap
(Source: Bahaloo-Horeh & Mousavi, 2020, p. 123186)
Identification of appropriate technologies
STRIDE elements are identified from assessment 2 which is an appropriate technique to diversify the threats. This technique is identified for the relevant threats and how to act against it.
? Spoofing is identified for Authentication security property.
? Tampering technique is for Integrity.
? Repudiation is a recommended threat key factor accessed by the CEO in a non-repudiation context (Laessoe, Jensen & Madeleine, 2017, 5).
? Information Disclosure might be considered for confidentiality.
? Denial of Service is considered for availability.
? Elevation of Privilege is an authorized technique involved in this case.
On the other hand, the DREAD model is a technique which is associated with risks/threats. NIST is also similar to these.
Conclusion
After discussing the threats, vulnerabilities in the B&C Insurance company, it is necessary to summarize those findings and outcomes that will be put forward in future cases. The course of actions must be recommended to mitigate potential threats in future are:
? Validating the threat and engaging the stakeholders.
? Conduct a proper risk management which may be beneficial and provide specific resolution to the existing threats.
? Beware of unreliable external networks, emails from the next time to prevent this kind of cybercrime scenario.
References
Armenia, S., Ferreira Franco, E., Nonino, F., Spagnoli, E., & Medaglia, C. M. (2019). Towards the definition of a dynamic and systemic assessment for cybersecurity risks. Systems Research and Behavioral Science, 36(4), 404–423. Retrieved on 18-Apr-2021 from, https://doi.org/10.1002/sres.2556
Bahaloo-Horeh, N., & Mousavi, S. M. (2020). Comprehensive characterization and environmental risk assessment of end-of-life automotive catalytic converters to arrange a sustainable roadmap for future recycling practices. Journal of Hazardous Materials, 400, 123186–123186. Retrieved on 19-Apr-2021 from, https://doi.org/10.1016/j.jhazmat.2020.123186
Boeke, S. (2018). National cyber crisis management: different European approaches. Governance, 31(3), 449–464. Retrieved on 19-Apr-2021 from, https://doi.org/10.1111/gove.12309
Camillo. (2017). Cybersecurity: risks and management of risks for global banks and financial institutions. Journal of Risk Management in Financial Institutions, 10(2), 196–200. Retrieved on 18-Apr-2021 from, https://lesa.on.worldcat.org/oclc/6998327984
Canfield, C. I., & Fischhoff, B. (2018). Setting priorities in behavioural interventions: an application to reducing phishing risk. Risk Analysis, 38(4), 826–838. Retrieved on 18-Apr-2021 from, https://doi.org/10.1111/risa.12917
Coburn, A., Leverett, E., & Woo, G. (2018). Solving cyber risk: protecting your company and society. John Wiley & Sons, Incorporated. Retrieved on 19-Apr-2021 from, https://lesa.on.worldcat.org/oclc/1080082434
Ganin, A. A., Quach, P., Panwar, M., Collier, Z. A., Keisler, J. M., Marchese, D., & Linkov, I. (2020). Multicriteria decision framework for cybersecurity risk assessment and management. Risk Analysis, 40(1), 183–199. Retrieved on 19-Apr-2021 from, https://doi.org/10.1111/risa.12891
Laessoe, U., Jensen, N. M. B., & Madeleine, P. (2017). Examination of the gait pattern based on adjusting and resulting components of the stride-to-stride variability: proof of concept. Bmc Research Notes, 10(1), 1–7. Retrieved on 19-Apr-2021 from, https://doi.org/10.1186/s13104-017-2623-8
Rytchkov, O., & Zhong, X. (2020). Information aggregation and p-hacking. Management Science, 66(4), 1605–1626. Retrieved on 19-Apr-2021 from, https://doi.org/10.1287/mnsc.2018.3259
Saia, R., & Carta, S. (2019). Evaluating the benefits of using proactive transformed-domain-based techniques in fraud detection tasks. Future Generation Computer Systems, 93, 18–32. Retrieved on 19-Apr-2021 from, https://doi.org/10.1016/j.future.2018.10.016
Wang, S. S. (2019). Integrated framework for information security investment and cyber insurance. Pacific-Basin Finance Journal, 57. Retrieved on 18-Apr-2021 from, https://doi.org/10.1016/j.pacfin.2019.101173
Zadeh, A. H., Jeyaraj, A., & Biros, D. (2020). Characterizing cybersecurity threats to organizations in support of risk mitigation decisions. E-Service Journal, 12(2), 1–34. Retrieved on 19-Apr-2021 from, https://lesa.on.worldcat.org/oclc/8978135163
Zheng, K., & Albert, L. A. (2019). A robust approach for mitigating risks in cyber supply chains. Risk Analysis, 39(9), 2076–2092. Retrieved on 19-Apr-2021 from, https://doi.org/10.1111/risa.13269

Download Samples PDF
Related Sample
- BUA4003 Principles of Economics Report 2
- ACCT6007 Financial Accounting Theory and Practice Report
- SOAD9206 Social Work Research in Practice Settings Report 1
- ACCY902 Forensic Accounting Assignment
- MBA6204 Quantitative Support of Decision Making Report
- HI6028 Finance Assignment
- MBA504 Data Analytics for Business Assignment
- BSBWOR502B Ensure Team Effectiveness Assignment
- CVE80010 Principles of Sustainability Report 3
- BUS1006 Business Law Assignment
- TCHR5003 Principles and Practices in Early Childhood Assignment
- Is AI Taking Over the Work of Financial Analysts
- STATS7061 Statistical Analysis Assignment
- TECH1100 Professional Practice and Communication Report 1
- COIT20245 Introduction To Programming Assignment
- ACCT6007 Financial Accounting Theory and Practice
- MGT602 Business Decision Making Process Case Study
- LB5236 International Political Economy Report
- MGT502 Business Communication
- MIS101 Information Systems for Business

Assignment Services
-
Assignment Writing
-
Academic Writing Services
- HND Assignment Help
- SPSS Assignment Help
- College Assignment Help
- Writing Assignment for University
- Urgent Assignment Help
- Architecture Assignment Help
- Total Assignment Help
- All Assignment Help
- My Assignment Help
- Student Assignment Help
- Instant Assignment Help
- Cheap Assignment Help
- Global Assignment Help
- Write My Assignment
- Do My Assignment
- Solve My Assignment
- Make My Assignment
- Pay for Assignment Help
-
Management
- Management Assignment Help
- Business Management Assignment Help
- Financial Management Assignment Help
- Project Management Assignment Help
- Supply Chain Management Assignment Help
- Operations Management Assignment Help
- Risk Management Assignment Help
- Strategic Management Assignment Help
- Logistics Management Assignment Help
- Global Business Strategy Assignment Help
- Consumer Behavior Assignment Help
- MBA Assignment Help
- Portfolio Management Assignment Help
- Change Management Assignment Help
- Hospitality Management Assignment Help
- Healthcare Management Assignment Help
- Investment Management Assignment Help
- Market Analysis Assignment Help
- Corporate Strategy Assignment Help
- Conflict Management Assignment Help
- Marketing Management Assignment Help
- Strategic Marketing Assignment Help
- CRM Assignment Help
- Marketing Research Assignment Help
- Human Resource Assignment Help
- Business Assignment Help
- Business Development Assignment Help
- Business Statistics Assignment Help
- Business Ethics Assignment Help
- 4p of Marketing Assignment Help
- Pricing Strategy Assignment Help
- Nursing
-
Finance
- Finance Assignment Help
- Do My Finance Assignment For Me
- Financial Accounting Assignment Help
- Behavioral Finance Assignment Help
- Finance Planning Assignment Help
- Personal Finance Assignment Help
- Financial Services Assignment Help
- Forex Assignment Help
- Financial Statement Analysis Assignment Help
- Capital Budgeting Assignment Help
- Financial Reporting Assignment Help
- International Finance Assignment Help
- Business Finance Assignment Help
- Corporate Finance Assignment Help
-
Accounting
- Accounting Assignment Help
- Managerial Accounting Assignment Help
- Taxation Accounting Assignment Help
- Perdisco Assignment Help
- Solve My Accounting Paper
- Business Accounting Assignment Help
- Cost Accounting Assignment Help
- Taxation Assignment Help
- Activity Based Accounting Assignment Help
- Tax Accounting Assignment Help
- Financial Accounting Theory Assignment Help
-
Computer Science and IT
- Operating System Assignment Help
- Data mining Assignment Help
- Robotics Assignment Help
- Computer Network Assignment Help
- Database Assignment Help
- IT Management Assignment Help
- Network Topology Assignment Help
- Data Structure Assignment Help
- Business Intelligence Assignment Help
- Data Flow Diagram Assignment Help
- UML Diagram Assignment Help
- R Studio Assignment Help
-
Law
- Law Assignment Help
- Business Law Assignment Help
- Contract Law Assignment Help
- Tort Law Assignment Help
- Social Media Law Assignment Help
- Criminal Law Assignment Help
- Employment Law Assignment Help
- Taxation Law Assignment Help
- Commercial Law Assignment Help
- Constitutional Law Assignment Help
- Corporate Governance Law Assignment Help
- Environmental Law Assignment Help
- Criminology Assignment Help
- Company Law Assignment Help
- Human Rights Law Assignment Help
- Evidence Law Assignment Help
- Administrative Law Assignment Help
- Enterprise Law Assignment Help
- Migration Law Assignment Help
- Communication Law Assignment Help
- Law and Ethics Assignment Help
- Consumer Law Assignment Help
- Science
- Biology
- Engineering
-
Humanities
- Humanities Assignment Help
- Sociology Assignment Help
- Philosophy Assignment Help
- English Assignment Help
- Geography Assignment Help
- Agroecology Assignment Help
- Psychology Assignment Help
- Social Science Assignment Help
- Public Relations Assignment Help
- Political Science Assignment Help
- Mass Communication Assignment Help
- History Assignment Help
- Cookery Assignment Help
- Auditing
- Mathematics
-
Economics
- Economics Assignment Help
- Managerial Economics Assignment Help
- Econometrics Assignment Help
- Microeconomics Assignment Help
- Business Economics Assignment Help
- Marketing Plan Assignment Help
- Demand Supply Assignment Help
- Comparative Analysis Assignment Help
- Health Economics Assignment Help
- Macroeconomics Assignment Help
- Political Economics Assignment Help
- International Economics Assignments Help
-
Academic Writing Services
-
Essay Writing
- Essay Help
- Essay Writing Help
- Essay Help Online
- Online Custom Essay Help
- Descriptive Essay Help
- Help With MBA Essays
- Essay Writing Service
- Essay Writer For Australia
- Essay Outline Help
- illustration Essay Help
- Response Essay Writing Help
- Professional Essay Writers
- Custom Essay Help
- English Essay Writing Help
- Essay Homework Help
- Literature Essay Help
- Scholarship Essay Help
- Research Essay Help
- History Essay Help
- MBA Essay Help
- Plagiarism Free Essays
- Writing Essay Papers
- Write My Essay Help
- Need Help Writing Essay
- Help Writing Scholarship Essay
- Help Writing a Narrative Essay
- Best Essay Writing Service Canada
-
Dissertation
- Biology Dissertation Help
- Academic Dissertation Help
- Nursing Dissertation Help
- Dissertation Help Online
- MATLAB Dissertation Help
- Doctoral Dissertation Help
- Geography Dissertation Help
- Architecture Dissertation Help
- Statistics Dissertation Help
- Sociology Dissertation Help
- English Dissertation Help
- Law Dissertation Help
- Dissertation Proofreading Services
- Cheap Dissertation Help
- Dissertation Writing Help
- Marketing Dissertation Help
- Programming
-
Case Study
- Write Case Study For Me
- Business Law Case Study Help
- Civil Law Case Study Help
- Marketing Case Study Help
- Nursing Case Study Help
- Case Study Writing Services
- History Case Study help
- Amazon Case Study Help
- Apple Case Study Help
- Case Study Assignment Help
- ZARA Case Study Assignment Help
- IKEA Case Study Assignment Help
- Zappos Case Study Assignment Help
- Tesla Case Study Assignment Help
- Flipkart Case Study Assignment Help
- Contract Law Case Study Assignments Help
- Business Ethics Case Study Assignment Help
- Nike SWOT Analysis Case Study Assignment Help
- Coursework
- Thesis Writing
- CDR
- Research


.png)
~5.png)
.png)
~1.png)























































.png)






